Anomaly Detection Challenges
Anomaly Detection Challenges
| Praktika | 6 SWS / 10 ECTS |
| Veranstalter: | |
| Zeit und Ort: | Mo, 16:00 – 17:30 Uhr, 01.06.011 |
| Beginn: | 2015-10-19 |
Updates
- Challenge 5 is published, as well as homework 7.
- Challenge 4 is published. This time we have a spam detection task, however in the fifth challenge we will be back to analyzing malware.
- As the deadline for challenge 3 is postponed, next class (07.12.) contains a tutorial in Bayesian Networks and Belief Propagation instead of student presentations.
- Challenge 3 is published
- Challenge 2 is published
- Challenge 1 is published and the participants have received invitations.
- Schedule for the course is published below. There will be 5 challenges and 7 short homeworks. Students have two weeks for each homework and challenge. For challenges there are presentation days, where students present and discuss their solutions. In addition to the presentation, students need to submit a short report about their solutions for each challenge, explaining what methods they used to solve their tasks. Deadline for each report is midnight before the presentation day.
- Kick-off meeting: 03.07.2015. at 14:30, room 01.08.033; Presentation from the meeting can be found here.
- How to apply?
- Select our course in the matching system
- Send us an e-mail with a very short CV, indicating your previous knowledge and experience relevant to the topic of the course (e.g. Machine Learning or IT Security course, internships, course projects...). This should be sent by 10.07. 12.07.2015. (update) to Bojan Kolosnjaji.
Schedule
| Date | Topic | Assignments |
| 19.10.2015. |
Intro to numpy Machine Learning in Python PDF, IPython Notebook, CSV
|
Homework 1
|
| 26.10.2015. |
From linear regression to SVM PDF, HW2, dataset1, dataset2 |
Homework 2 & Challenge 1 |
| 02.11.2015. |
Approaches in anomaly detection PDF, HW3 |
Homework 3 |
| 09.11.2015. | Presentation day for challenge 1 | Challenge 2 |
| 16.11.2015. |
Semi-supervised Learning PDF, HW4 |
Homework 4 |
| 23.11.2015. |
Introduction to malware analysis systems Ensemble Learning PDF, HW5 |
Challenge 3 |
| 30.11.2015. | Presentation day for challenge 2 | Homework 5 |
| 07.12.2015. |
Bayesian Networks, Belief Propagation PDF HW6 |
Homework 6 |
|
14.12.2015. |
Presentation day for challenge 3 | Challenge 4 |
| 21.12.2015. |
Belief Propagation 2 HW7 (deadline 17.01.)
|
Challenge 5 |
| 11.01.2016. |
Deep Learning for anomaly detection Presentation day for challenge 4 |
None |
| 18.01.2016. | Presentation day for challenge 5 | None |
Description
In information security domain, anomaly detection gains its own importance from researchers day by day. It is discovered that occasionally emerged frauds or intrusions in modern information systems have incurred significant loss when the suspicious activities were not detected or inefficiently processed. Therefore, numerous efforts have been devoted to devise effective detection methods, and then proceed to automation of anomaly identification in real time. In this practical course, we challenge students with a set of well designated learning tasks, which require the participants to understand the task scenario entirely and to design their own algorithms to identify corresponding anomalies. A competition on discovering the anomalies will be conducted based on the performance of their algorithms.
Requirement
- Basic knowlege of Machine learning and data mining
- Good programming skills
- Basic knowlege in Python
- Registered Master or Diplom students in Informatics or a similar area
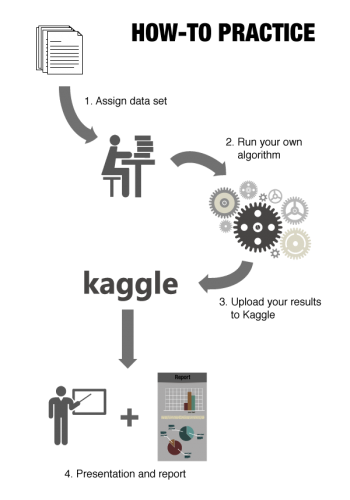
Instruction
Contact
Bojan Kolosnjaji
Email: kolosnjaji@sec.in.tum.de
Room: 01.08.061
Huang Xiao
Email: xiaohu@in.tum.de
Room: 01.08.057
George Webster
Email: webstergd@sec.in.tum.de
